Cybersecurity news and articles

7 antivirus myths that are dead wrong www.pcworld.com | Today
Keywords: crypto, virus, cryptocurrency, game, container
Mac Virus Scan: How to protect your Mac from malware www.macworld.com | Yesterday
Keywords: virus, network, database, test, security

DPRK Hackers Compromise South Korean Defense Contractors www.cysecurity.news | Today
Keywords: cryptocurrency, bitcoin, design, malware, security

Hackers Utilize Antivirus Update Mechanism to Deploy GuptiMiner Malware www.cysecurity.news | Today
Keywords: virus, cryptocurrency, cpu, malware, security

Minding the cybersecurity talent gap for MSPs smartermsp.com | Yesterday
Keywords: artificial intelligence, cloud computing, computing

'ArcaneDoor' Cyberspies Hacked Cisco Firewalls To Access Government Networks it.slashdot.org | Yesterday
Keywords: security, malware, network, cybersecurity

Innovations in Fraud Detection: Exploring Cutting-edge Technologies and Solutions iotbusinessnews.com | Yesterday
Keywords: iot, big data, machine learning

Banking Malware "Brokewell" Hacks Android Devices, Steals User Data www.cysecurity.news | Today
Keywords: malware, security, cybercriminal, android

As romance scams soar, the dark world of cyber slaves is exposed metro.co.uk | Yesterday
Keywords: scam, mobile

Is Your VPN Safe? Or Can It be Hacked? www.cysecurity.news | Yesterday
Keywords: network, excel, security, crypto, cybercriminal
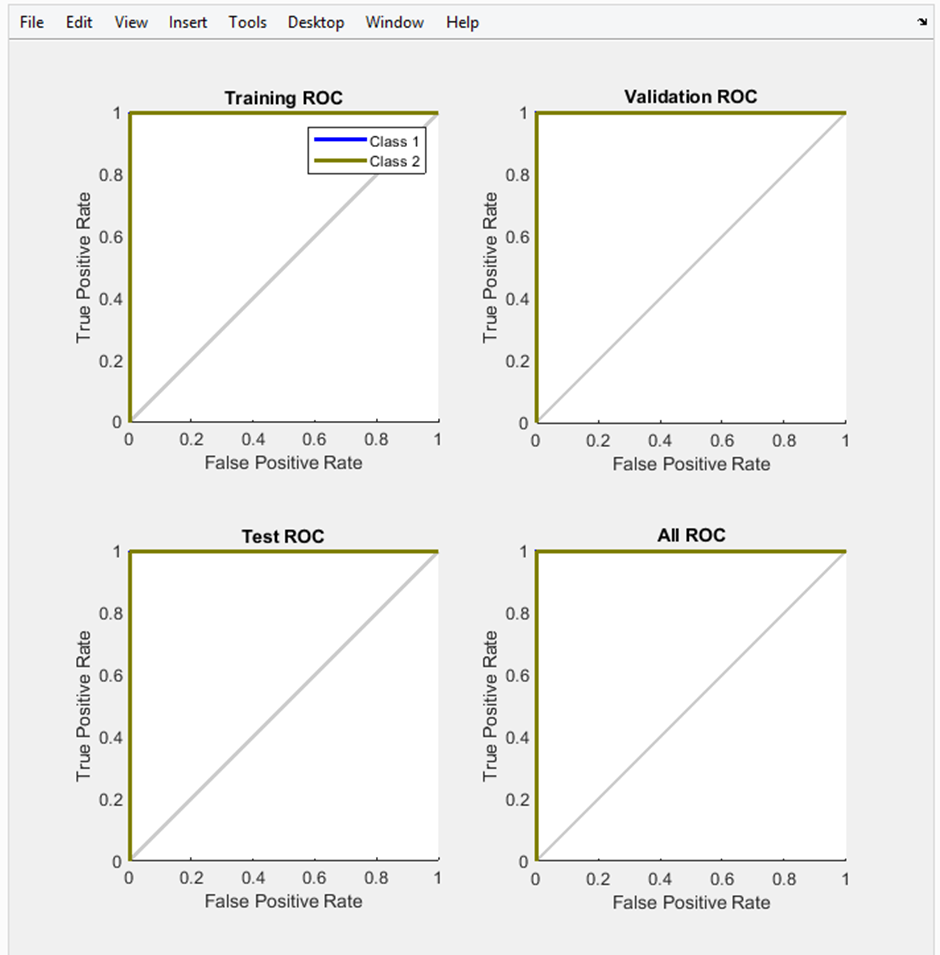
Smart Mobile Telecommunication Network Fraud Detection System Using Call Traffic Pattern Analysis and Ar... article.sapub.org | Yesterday
Keywords: neural network, network, machine learning
Hackers have been abusing a popular antivirus solution to crack corporate networks for five years www.itpro.com | Yesterday
Keywords: network, virus
Keywords: coding, human interface, optimization, react

Google Faces Challenges with Scam Ads Mimicking Big Brands And Platforms (Including Meta's Facebook) www.digitalinformationworld.com | Today
Keywords: ai , malware, security, scam

Thoma Bravo to buy UK cybersecurity company Darktrace for $5bn www.verdict.co.uk | Today
Keywords: ai , cybersecurity, security, network

7 antivirus myths that are dead wrong www.pcworld.com | Today
Mac Virus Scan: How to protect your Mac from malware www.macworld.com | Yesterday

DPRK Hackers Compromise South Korean Defense Contractors www.cysecurity.news | Today

Hackers Utilize Antivirus Update Mechanism to Deploy GuptiMiner Malware www.cysecurity.news | Today

Minding the cybersecurity talent gap for MSPs smartermsp.com | Yesterday

'ArcaneDoor' Cyberspies Hacked Cisco Firewalls To Access Government Networks it.slashdot.org | Yesterday

Innovations in Fraud Detection: Exploring Cutting-edge Technologies and Solutions iotbusinessnews.com | Yesterday

Banking Malware "Brokewell" Hacks Android Devices, Steals User Data www.cysecurity.news | Today

As romance scams soar, the dark world of cyber slaves is exposed metro.co.uk | Yesterday

Is Your VPN Safe? Or Can It be Hacked? www.cysecurity.news | Yesterday
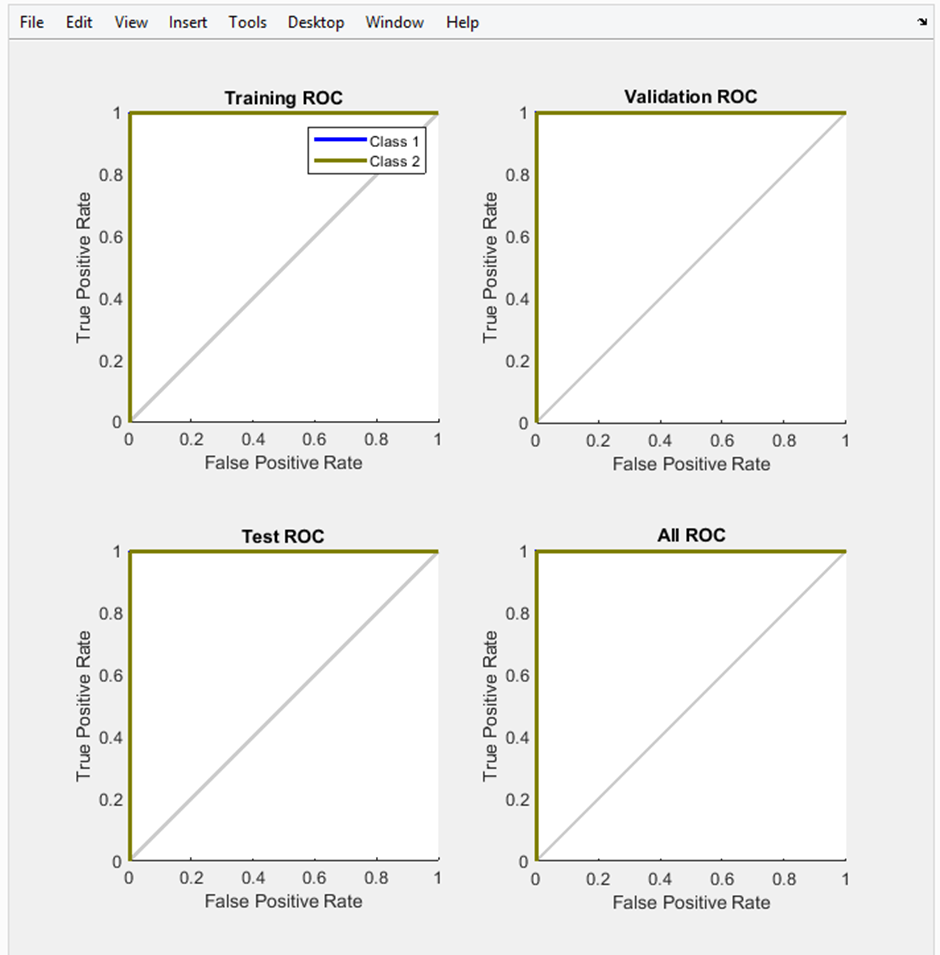
Smart Mobile Telecommunication Network Fraud Detection System Using Call Traffic Pattern Analysis and Ar... article.sapub.org | Yesterday
Hackers have been abusing a popular antivirus solution to crack corporate networks for five years www.itpro.com | Yesterday

Google Faces Challenges with Scam Ads Mimicking Big Brands And Platforms (Including Meta's Facebook) www.digitalinformationworld.com | Today

Thoma Bravo to buy UK cybersecurity company Darktrace for $5bn www.verdict.co.uk | Today
